Iranian Actors Sell Critical Infrastructure Access, Bumblebee Returns with New Threats, 108 Firms Leaked with Professional Services Most Affected, and CISA Adds Microsoft, ScienceLogic, and Veeam Vulnerabilities
In our latest Cyber Intelligence Brief, Deepwatch ATI looks at new threats and techniques to deliver actionable intelligence for SecOps organizations.
Each week we look at in-house and industry threat intelligence and provide ATI analysis and perspective to shine a light on a spectrum of cyber threats.
Iranian Actors Selling Access to Critical Infrastructure
The Rundown
Iranian cyber actors are selling access to critical infrastructure, fueling a global cybercrime market, and putting essential systems at risk.
This growing threat compromises sensitive data and exposes infrastructure to potential further attacks, making it a pressing issue for organizations worldwide to strengthen their cybersecurity defenses.
Source Material: CISA
Bumblebee Returns: New Campaign Poses Fresh Risks to Businesses
The Rundown
A new Bumblebee malware campaign has surfaced for the first time since Europol’s crackdown in May, marking a critical resurgence that threatens businesses globally with various malware, like ransomware and infostealers.
This resurgence signals that major cyber threats like Bumblebee, while disrupted, can reappear, putting organizations at risk of catastrophic data breaches and ransomware attacks despite previous large-scale takedowns.
Source Material: Netskope
Leak Sites: 108 Firms Listed, Professional Services Tops the List
The Rundown
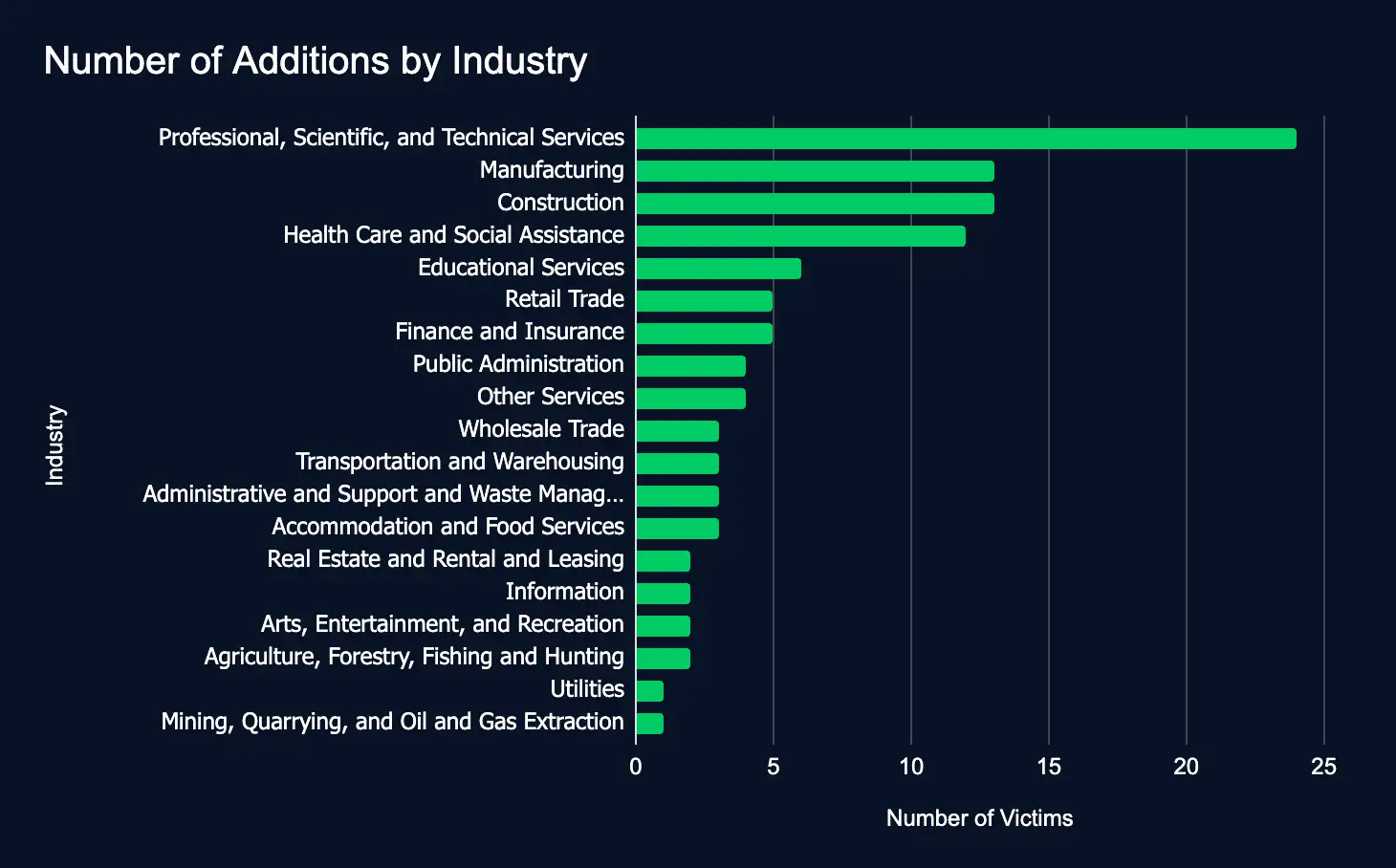
In just one week, 108 organizations listed across 19 industries were added to ransomware and data leak sites, a decrease of 5 organizations from last week.
This week, critical sectors like professional services, manufacturing, and construction were listed the most, emphasizing the urgent need for robust cybersecurity measures to protect sensitive data and operations worldwide.
CISA Adds Microsoft, ScienceLogic, and Veeam Vulnerabilities to Exploited List
The Rundown
Between October 17th and 23rd, three critical vulnerabilities affecting Microsoft, ScienceLogic, and Veeam products were added to CISA’s Known Exploited Vulnerabilities catalog. If not addressed swiftly, these vulnerabilities could expose organizations to potential cyberattacks.
These newly cataloged vulnerabilities highlight looming risks for organizations using widespread technologies. Failure to patch these flaws could lead to remote code execution or even ransomware attacks. If state-sponsored and cybercriminal attackers focus on these weaknesses, timely action will be crucial to prevent exploitation.
Recommendations
ATI recommends mitigative action occur according to the mitigation “Due Date” recommended by CISA.
Source Material: CISA
What We Mean When We Say
Estimates of Likelihood
We use probabilistic language to reflect the Intel Team’s estimates of the likelihood of developments or events because analytical judgments are not certain. Terms like “probably,” “likely,” “very likely,” and “almost certainly” denote a higher than even chance. The terms “unlikely” and “remote” imply that an event has a lower than even chance of occurring; they do not imply that it will not. Terms like “might” reflect situations where we are unable to assess the likelihood, usually due to a lack of relevant information, which is sketchy or fragmented. Terms like “we can’t dismiss,” “we can’t rule out,” and “we can’t discount” refer to an unlikely, improbable, or distant event with significant consequences.
Confidence in Assessments
Our assessments and projections are based on data that varies in scope, quality, and source. As a result, we assign our assessments high, moderate, or low levels of confidence, as follows:
High confidence indicates that our decisions are based on reliable information and/or that the nature of the problem allows us to make a sound decision. However, a “high confidence” judgment is not a fact or a guarantee, and it still carries the risk of being incorrect.
Moderate confidence denotes that the information is credible and plausible, but not of high enough quality or sufficiently corroborated to warrant a higher level of assurance.
Low confidence indicates that the information’s credibility and/or plausibility are in doubt, that the information is too fragmented or poorly corroborated to make solid analytic inferences, or that we have serious concerns or problems with the sources.

Share