FortiManager Zero-Day Exploited for Data Theft, ClickFix Campaign Threatens Organizations, 162 Firms Leaked with Manufacturing Most Affected, and CISA Adds Cisco, Roundcube, and Fortinet Vulnerabilities
In our latest Cyber Intelligence Brief, Deepwatch ATI looks at new threats and techniques to deliver actionable intelligence for SecOps organizations.
Each week we look at in-house and industry threat intelligence and provide ATI analysis and perspective to shine a light on a spectrum of cyber threats.
Attackers Exploit FortiManager Zero-Day (CVE-2024-47575) for Data Theft
The Rundown
Attackers have exploited a zero-day vulnerability in FortiManager devices (CVE-2024-47575), bypassing access controls to exfiltrate configuration files containing users’ FortiOS SHA256-hashed passwords.
With FortiManager’s widespread use in managing network security, this vulnerability exposes organizations to potential attacks and requires immediate attention. Successful exploitation has the potential to deepen access, pivot across managed networks, and data theft.
Source Material: Mandiant
ClickFix Campaign Threats to Organizations
The Rundown
Deepwatch Threat Intel team assesses that cybercriminals will likely continue using the ClickFix technique to target organizations and individuals, seeking to manipulate end-users into executing malicious commands that deploy malware. By leveraging social engineering tactics, attackers aim to steal credentials and create a persistent foothold within targeted networks.
The broad range of attack vectors utilized suggests a coordinated effort, likely intended to achieve widespread distribution of information stealers, remote access trojans (RATs), and other malware to disrupt and compromise operational security.
The ClickFix technique is a social engineering tactic employed by cybercriminals to deceive users into downloading malware through fake CAPTCHAs, error messages, and prompts that entice users to inadvertently run malicious PowerShell scripts and commands. Campaigns often lead users to compromised or fraudulent websites, which present pop-up messages or overlay warnings suggesting a system error.
Victims unknowingly copy and paste a script into PowerShell, which ultimately deploys and executes malware, such as stealer programs (e.g., Lumma Stealer) or loaders (e.g., Amadey Loader), to access sensitive information or establish a persistent presence on the victim’s system.
Source Material: Securelist, Securi, Proofpoint, Sekoia, and Godaddy
Leak Sites: 162 Firms Listed, Manufacturing Tops the List
The Rundown
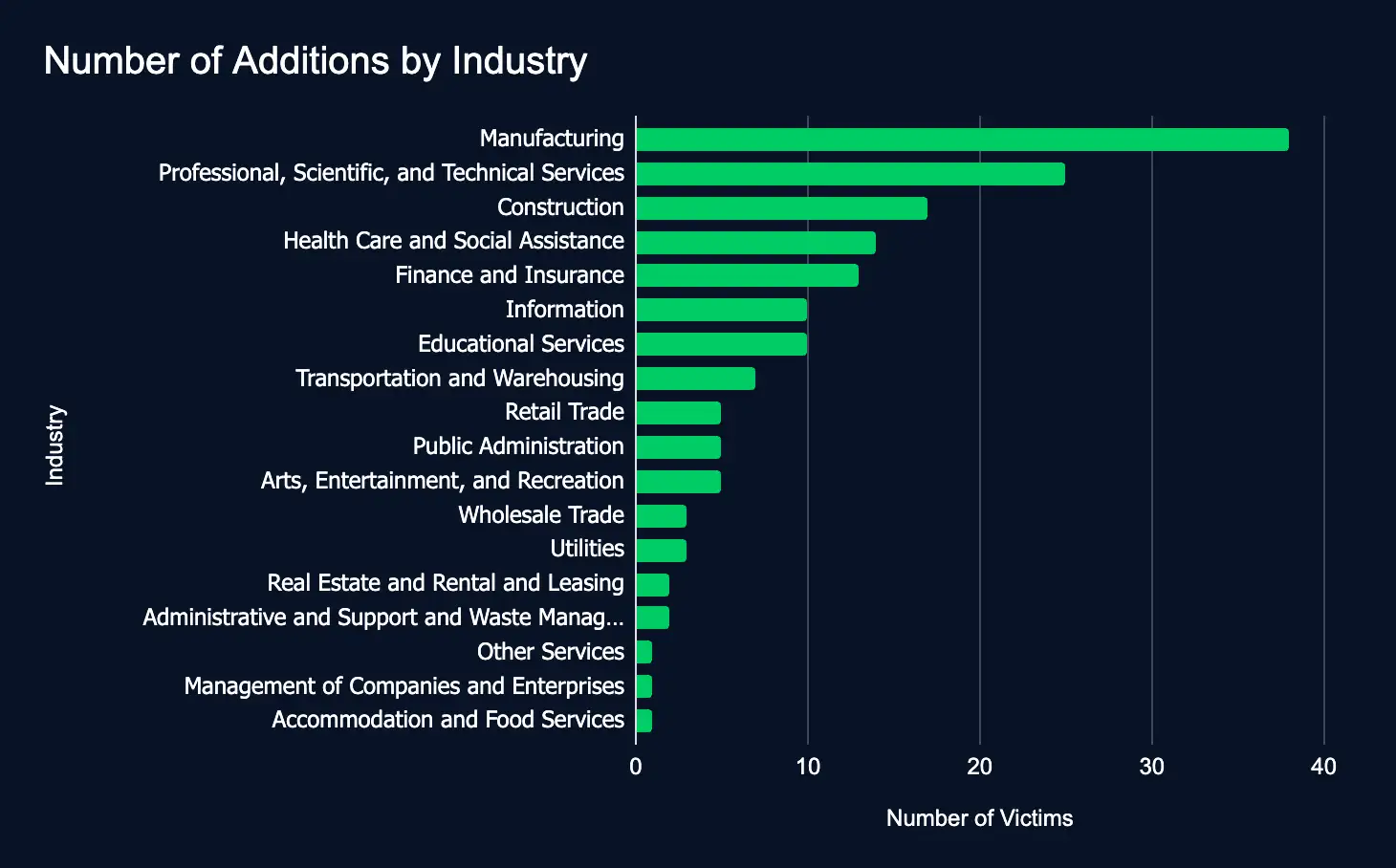
In just one week, 162 organizations listed across 18 industries were added to ransomware and data leak sites, an increase of 54 organizations from last week.
This week, critical sectors like Manufacturing, Professional Services, and Construction were listed the most, emphasizing the urgent need for robust cybersecurity measures to protect sensitive data and operations worldwide.
CISA Adds Cisco, Roundcube, and Fortinet Vulnerabilities to Exploited List
The Rundown
Between October 23 and October 30, three critical vulnerabilities affecting Cisco (CVE-2024-20481), RoundCube (CVE-2024-37383), and Fortinet (CVE-2024-47575) products were added to CISA’s Known Exploited Vulnerabilities catalog. If not addressed swiftly, these vulnerabilities could expose organizations to potential cyberattacks.
These newly cataloged vulnerabilities highlight looming risks for organizations using widespread technologies. Failure to patch these flaws could lead to denial of service or code execution. If state-sponsored and cybercriminal attackers focus on these weaknesses, timely action will be crucial to prevent exploitation.
Recommendations
ATI recommends mitigative action occur according to the mitigation “Due Date” recommended by CISA.
Source Material: CISA
What We Mean When We Say
Estimates of Likelihood
We use probabilistic language to reflect the Intel Team’s estimates of the likelihood of developments or events because analytical judgments are not certain. Terms like “probably,” “likely,” “very likely,” and “almost certainly” denote a higher than even chance. The terms “unlikely” and “remote” imply that an event has a lower than even chance of occurring; they do not imply that it will not. Terms like “might” reflect situations where we are unable to assess the likelihood, usually due to a lack of relevant information, which is sketchy or fragmented. Terms like “we can’t dismiss,” “we can’t rule out,” and “we can’t discount” refer to an unlikely, improbable, or distant event with significant consequences.
Confidence in Assessments
Our assessments and projections are based on data that varies in scope, quality, and source. As a result, we assign our assessments high, moderate, or low levels of confidence, as follows:
High confidence indicates that our decisions are based on reliable information and/or that the nature of the problem allows us to make a sound decision. However, a “high confidence” judgment is not a fact or a guarantee, and it still carries the risk of being incorrect.
Moderate confidence denotes that the information is credible and plausible, but not of high enough quality or sufficiently corroborated to warrant a higher level of assurance.
Low confidence indicates that the information’s credibility and/or plausibility are in doubt, that the information is too fragmented or poorly corroborated to make solid analytic inferences, or that we have serious concerns or problems with the sources.

Share