Critical Ivanti Vulnerability CVE-2024-29847 Exposed, WhatsUp Gold Targeted, Azure Storage Tool Misused for Data Theft, 72 Firms Leaked, and CISA Adds Major Vendor Vulnerabilities
In our latest Cyber Intelligence Brief, Deepwatch ATI looks at new threats and techniques to deliver actionable intelligence for SecOps organizations.
Each week we look at in-house and industry threat intelligence and provide ATI analysis and perspective to shine a light on a spectrum of cyber threats.
Contents
- Advisory | POC Released for Critical Ivanti Vulnerability CVE-2024-29847
- Attackers Target WhatsUp Gold, Execute Malicious Code
- Ransomware Actors Turn Azure Storage Tool into Data Theft Weapon
- 72 Firms Listed on Data Leak Sites in a Week: Manufacturing Tops the List
- CISA Adds Adobe, Apache, Ivanti, Microsoft, Oracle, and Progress Vulnerabilities to Exploited List
POC Released for Critical Ivanti Vulnerability CVE-2024-29847
The Rundown
A proof-of-concept (POC) exploit has been released for a critical Ivanti Endpoint Manager vulnerability, CVE-2024-29847, exposing systems to potential remote code execution.
Attackers could weaponize the POC exploit code to exploit the vulnerability to install malware, such as a web shell, posing a severe risk to sensitive data and operations. Even with a patch available, the release of exploit code makes swift action by organizations crucial to prevent breaches.
Read our Customer Advisory on this event.
Attackers Target WhatsUp Gold, Execute Malicious Code
The Rundown
Attackers may have leveraged newly discovered vulnerabilities in WhatsUp Gold, a popular network monitoring tool, to gain access and execute malicious PowerShell scripts within hours of a proof-of-concept release.
Organizations running outdated versions of WhatsUp Gold may face significant security risks. The exploited flaws allow unauthorized access to encrypted credentials and may facilitate code execution, which could lead to widespread network compromise.
Source Material: Trend Micro
Ransomware Actors Turn Azure Storage Tool into Data Theft Weapon
The Rundown
Ransomware groups like BianLian and Rhysida have abused Microsoft’s Azure Storage Explorer to steal sensitive data, transforming a benign tool into a powerful weapon for large-scale data exfiltration.
Cybercriminals’ repurposing of Azure Storage Explorer signals a troubling new frontier in ransomware attacks, where legitimate cloud management tools are now being leveraged for data theft. Understanding and identifying these tactics is essential for organizations to strengthen their defenses against evolving cyber threats.
Source Material: modePUSH
72 Firms Listed on Data Leak Sites in a Week: Manufacturing Tops the List
The Rundown
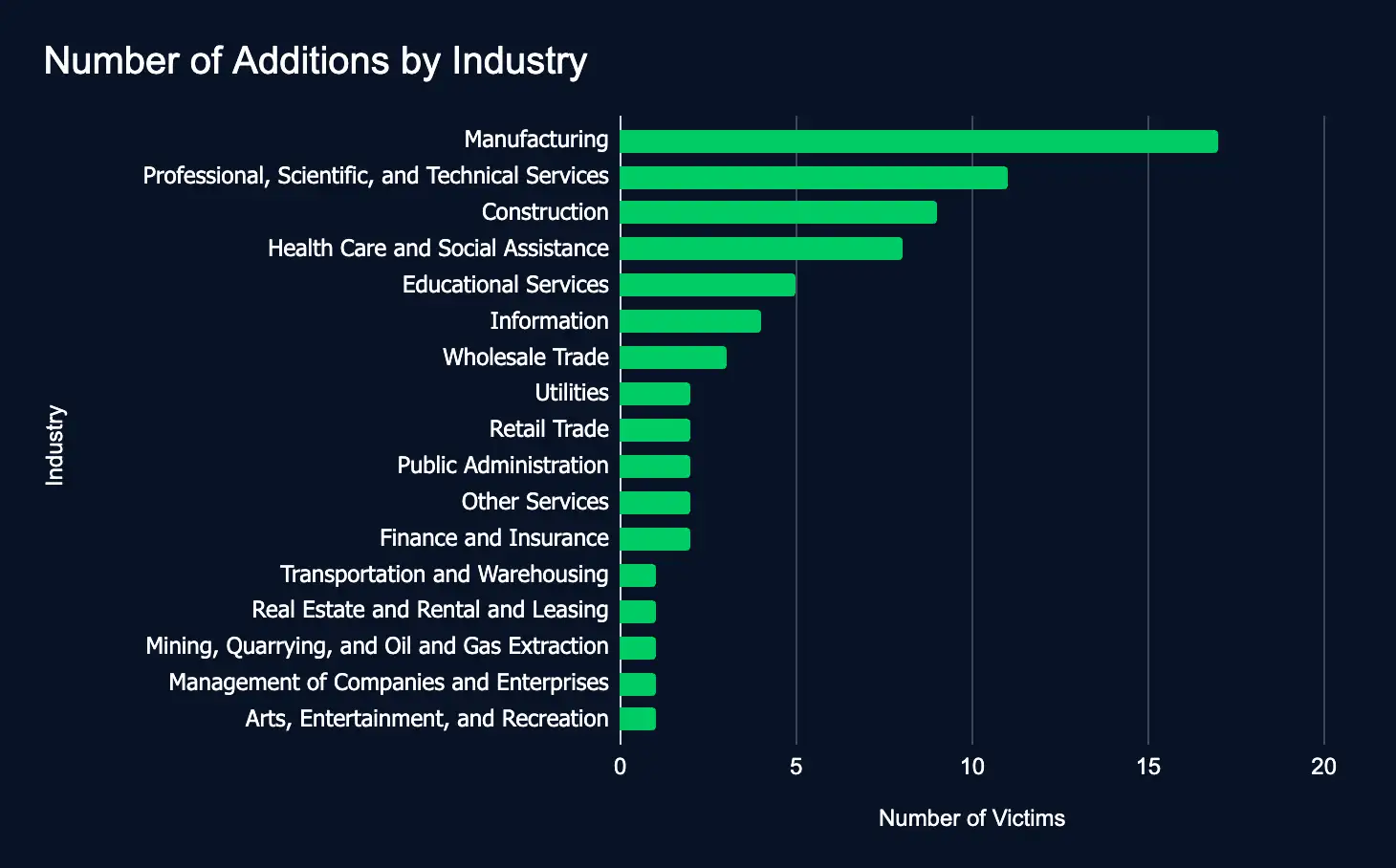
Between September 9 and 15, ransomware groups added 72 new organizations, spanning 17 industries and 19 countries, to data leak sites, with the US and manufacturing sectors listed the most.
Compared to last week, the slight increase in additions highlights a growing threat to critical industries and global operations, emphasizing the urgent need for enhanced cybersecurity across sectors vulnerable to data leaks and extortion.
CISA Adds Adobe, Apache, Ivanti, Microsoft, Oracle, and Progress Vulnerabilities to Exploited List
The Rundown
The Cybersecurity and Infrastructure Security Agency (CISA) has added 12 vulnerabilities affecting Adobe, Apache, Ivanti, Microsoft, Oracle, and Progress products to its catalog of known exploited vulnerabilities, warning of potential threats if these are left unpatched.
These vulnerabilities target widely used systems across industries. If not addressed, they pose significant risks to data integrity and network security, potentially allowing attackers to remotely execute code or gain unauthorized access. Organizations must act and apply the necessary updates and mitigations before the recommended deadlines.
Recommendations
ATI recommends mitigative action occur according to the mitigation “Due Date” recommended by CISA.
Source Material: CISA
What We Mean When We Say
Estimates of Likelihood
We use probabilistic language to reflect the Intel Team’s estimates of the likelihood of developments or events because analytical judgments are not certain. Terms like “probably,” “likely,” “very likely,” and “almost certainly” denote a higher than even chance. The terms “unlikely” and “remote” imply that an event has a lower than even chance of occurring; they do not imply that it will not. Terms like “might” reflect situations where we are unable to assess the likelihood, usually due to a lack of relevant information, which is sketchy or fragmented. Terms like “we can’t dismiss,” “we can’t rule out,” and “we can’t discount” refer to an unlikely, improbable, or distant event with significant consequences.
Confidence in Assessments
Our assessments and projections are based on data that varies in scope, quality, and source. As a result, we assign our assessments high, moderate, or low levels of confidence, as follows:
High confidence indicates that our decisions are based on reliable information and/or that the nature of the problem allows us to make a sound decision. However, a “high confidence” judgment is not a fact or a guarantee, and it still carries the risk of being incorrect.
Moderate confidence denotes that the information is credible and plausible, but not of high enough quality or sufficiently corroborated to warrant a higher level of assurance.
Low confidence indicates that the information’s credibility and/or plausibility are in doubt, that the information is too fragmented or poorly corroborated to make solid analytic inferences, or that we have serious concerns or problems with the sources.

Share